Ramping up the cyberforces
Photo by Kathy F. Atkinson November 23, 2016
UD's new Cyber Range adds strategic proving ground to expanding cybersecurity program
It's that ho-ho-ho season again. Shopping carts are filling up, money is changing hands and shady characters are looking for easy targets.
With most merchants offering online options and Cyber Monday deals, there are renewed calls to use strong passwords, keep software updated and resist email scams. Those are basic safeguards – as important as locking the doors of your house and not leaving 50 million copies of the key lying around outside.
The roots of many cyberthreats extend to a murky and technically sophisticated underworld where government regulators are not on duty, no one wears an ID badge and the workforce includes faceless (ro)bots connected in a vast network of servers, clouds and indecipherable code.
It takes complex mathematical knowledge, deep understanding of encryption strategies, skilled engineers and computer scientists to counter such efforts.
The University of Delaware is contributing to that work with a growing menu of cybersecurity studies including a graduate-level degree program, an undergraduate minor, online options, a certificate program and classes at Aberdeen (Maryland) Proving Ground.
With all of that, UD has just been designated a National Center of Academic Excellence in Cyber Defense by the National Security Agency (NSA) and the U.S. Department of Homeland Security.
This spring, the University expects to open its new Cyber Range, a dedicated space for students to develop and practice skills in a variety of scenarios and "capture-the-flag" type exercises where they can test programs for security flaws, build coding skills, respond to attacks and learn counter measures.
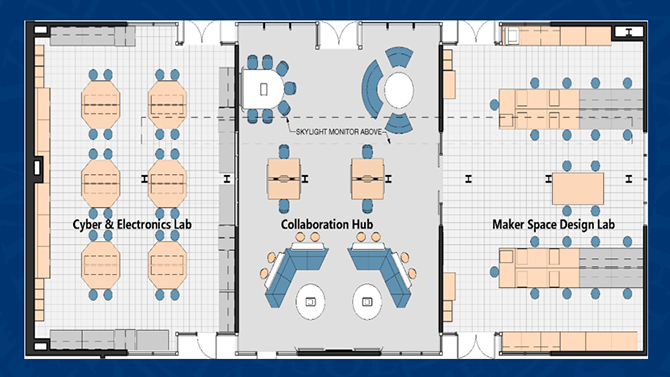
The Cyber Range is part of UD's new 4,500-square-foot "iSuite" (the "i" stands for innovation) under construction in Evans Hall. The three-room suite – supported, in part, by a $1 million grant from the state of Delaware – connects cyberthinkers with a workshop and a collaborative middle ground where ideas and expertise can cross traditional boundary lines.
That's comfortable territory for Chase Cotton, professor and director of UD's Center for Information and Communications Sciences. Cotton knows the math, the gadgets and the industrial demand for cybersavvy employees. Before joining the UD faculty in 2008, he spent years building global internet systems and leading teams of engineers in technical companies. He now helps students imagine, design and build innovative devices and solutions with security in mind.
"We think almost every engineer and scientist should have an introduction to this, at least," Cotton said.
The University's tactical approach to cybersecurity includes multiple fronts – educating and training students and workers, doing the research that will expand knowledge in the field and building partnerships with government, industry and military practitioners.
National defense expert Starnes Walker, founding director of the UD Cybersecurity Initiative, has a key role in developing those partnerships, with his background in nuclear physics, industry and senior cybersecurity management positions in the U.S. departments of Defense, Energy and Homeland Security.
He was among the invited panelists at a recent cybersecurity summit hosted by MIT, where he talked about the shared responsibilities of government, industry and academia and the need for each to bring their capabilities to bear on the problem.
"The role of academia is to come up with solutions that are cost-effective, implemented easily and fit into legacy operations," Walker said. "The best way to do all of that is to form a partnership of collaborators."
Taking a broad perspective on security is essential, Cotton said, looking not only at computer security but also at product design and what new threats may be on the horizon.
Industry leaders want employees with the kind of training that allows them to immediately sit down at a keyboard, fight attackers off and defend the perimeter, Cotton said.
The Cyber Range will give students opportunities to face realistic attacks – the kind they may encounter in a job setting.
But the NSA's concern is that security systems that work today are not going to survive, Cotton said. Someone must prepare for that, too, even though no one knows now what "that" will include.
Andrew Novocin, on the faculty in the Department of Electrical and Computer Engineering, does that kind of mathematical and computational thinking and the students in his classes, clubs and other collaborations come away with insights in business and marketing, too.
He is working to position UD students as the best possible candidates for this emerging job market.
"He's a dual threat," Cotton said of Novocin. "He is one of the best practicing computer scientists I've ever met. We were lucky to get him."
Novocin keeps a fast pace, teaching classes with names like "Intro to Lattice-Based (Post-Quantum) Crypto" while also building a new Cyber Scholars program to develop leaders in cybersecurity across all majors, offering frequent "crash courses" in all aspects of computing, security and web development, steering mini-hackathons and directing UD's Vertically Integrated Projects – VIPs, for short – a new endeavor that connects students, postdocs and faculty in fields they have in common, such as energy, health or cybersecurity. He is leading the VIP "crypto-cloud" team, which is working on better encryption for cloud computing.
Novocin also works on many layers of security for financial services and health information, including such things as serverless systems, so-called because they allow companies to scale up businesses that deal with sensitive data without the need to use their own servers. He is working to get an ATM in his lab so students can explore it and develop better security methods.
Among other projects, Novocin's students are developing a cybersecurity consultancy for small businesses that want to avoid a devastating hack but don't have the personnel to shore up their defenses.
Attacks are done for reasons other than financial gain, of course. They may be designed to take control of systems or gain access to sensitive data.
Trade secrets and intellectual property are high-value targets, said Kenneth Barner, professor and chairman of the Department of Electrical and Computer Engineering.
"Developing a new airplane costs billions of dollars," he said. "For a fraction of that, you can steal those plans."
Walker points to other systemic problems, such as those found in refineries, which may have 7,000 different devices working.
"We have legacy hardware systems and software, each with certain vulnerabilities," Walker said, "and that collective vulnerability introduces all sorts of other vulnerabilities. Where you have layered legacy systems, you have seams and those seams are where the vulnerability exists. How do you shore up a system for cyber vulnerabilities in a reasonable and prioritized way? How do you keep enhancing the cybersecurity, reducing vulnerability and improving the performance of the network and operations?"
The research potential is extensive and Haining Wang, a professor who studies network and cloud security, is leading that part of UD's strategy.
UD Provost Domenico Grasso has provided funding for six interdisciplinary grants in 2016.
And recruiting is underway for UD's first cohort of Cyber Scholars, a competitive program that will include technical studies along with ethics, policy and behavioral and criminology components.
"We are at the frontier stage," Novocin said. "A lot is going on."
Contact Us
Have a UDaily story idea?
Contact us at ocm@udel.edu
Members of the press
Contact us at mediarelations@udel.edu or visit the Media Relations website