Digital defenses
Cybersecurity expert Hathaway discusses risks of modern digital world
1:50 p.m., April 12, 2012--The near future of digital technology could allow citizens to turn on their toaster ovens via the Internet from just about anywhere, but these developments could pose serious threats to individuals’ safety, according to a cybersecurity expert.
Melissa Hathaway, a former senior director for cyberspace in the National Security Council, highlighted examples of the threats the Internet has created for both national and personal security during a University of Delaware Global Agenda speaker series presentation on Wednesday night, April 11, in Mitchell Hall.
Video of the presentation is available at this website.
People Stories
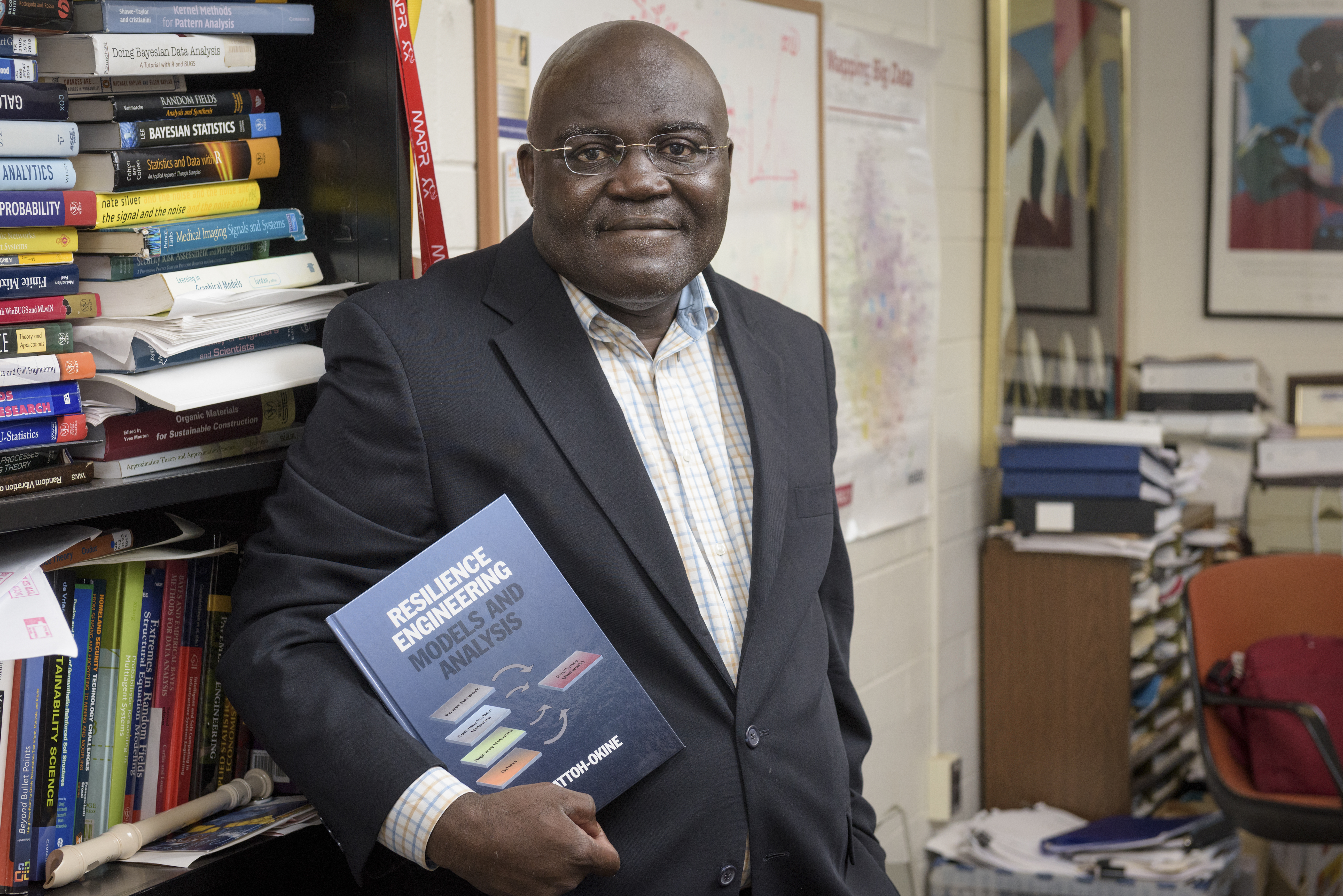
'Resilience Engineering'
Reviresco June run
Hathaway said cybersecurity initiatives at the government level were originally developed to help protect key businesses in the United States from intellectual property theft. She said a small flash drive or writable DVD has the potential to steal billions of dollars worth of data from companies or, in the case of Wikileaks, hundreds of thousands of classified government documents.
She said issues arising from new technologies were shocking to the intelligence community because they changed the direction security agencies had to monitor. “We were never looking for the inside going out, we were always looking for the outside coming in,” Hathaway said.
Hathaway said the example of Stuxnet, a cyberbug that shut down centrifuges at an Iranian nuclear power plant, illustrated the potential of weaponry being derived from Internet-based technology. She said the Stuxnet bug has since been replicated several times over, and countries like the United States are vulnerable to attacks through this medium.
She said cyberthreats have also arisen from the dependence the modern world now has on the Internet and automated technology, including in the operation of electrical or water systems. She said these essential resources could be compromised if computer viruses infiltrated the system, or simply if the technology malfunctioned.
Hathaway said she and her son observed an example of technology dependence while shopping for Legos on Christmas Eve, a gift they were unable to purchase because the store’s computer server shut down. Hathaway’s young son questioned the inability of the store to continue operating.
“He said, ‘Well, Mommy, we’re not a very advanced society if we can’t go backwards,'” Hathaway said.
And the Internet, Hathaway said, does not only pose threats to the security of government or business information; personal security in the virtual world has also been compromised with advancing technology.
Hathaway said credit card theft is “alive and well,” and the increased cost of faulty transactions for the companies has resulted in higher interest rates for consumers. Popular video gaming networks also have the potential to be infiltrated by criminals attempting to steal credit or Social Security information, even from young children and teenagers playing the games.
She said criminals are able to gain access to personal information, such as account passwords or even Social Security numbers, by embedding “back door” software into smart phone and computer applications or structurally implanting the corrupt technology into the hardware.
An example of the theft capabilities of cybertechnology came when malware was installed in the motherboards of Dell computers, which Hathaway said opened the systems up to allow transmission of personal passwords to the criminals who had embedded the malware.
Hathaway said while communicating with strangers was avoided in the past, the Internet has resulted in people inadvertently letting others into their private lives. She said cyberstalking has become far easier through developments in computer and mobile applications. One smartphone application allows users to gain personal information about women who have “checked in” to the same location through a popular location-sharing mobile app.
With the number of young people using this type of technology, Hathaway said she hopes parents and adults begin to teach children about the potential dangers posed by the Internet. “We need to have digital education that brings the thought of right and wrong to this new age,” Hathaway said.
About Global Agenda
The theme of the spring Global Agenda series is "Spies, Lies and Sneaky Guys: Espionage and Intelligence in the Digital Age."
Global Agenda is presented by the Institute for Global Studies, the Department of Communication, the Department of Political Science and International Relations and the Center for Political Communication.
Talks are moderated by Ralph Begleiter, director of the Center for Political Communication.
Presentations are held at 7:30 p.m., Wednesdays, in Mitchell Hall and are free and open to the public.
The spring series will conclude on May 2 with "The Future of Intelligence and Espionage," featuring Matthew M. Aid, a leading intelligence historian and expert on the National Security Agency.
Aid was instrumental in exposing that U.S. intelligence agencies had been improperly "reclassifying" and removing documents from the National Archives to keep them secret. He is a Russian linguist and author of Intel Wars: The Secret History of the Fight Against Terror (2012), Secret Sentry: The Untold History of the National Security Agency (2009) and co-editor of Secrets of Signals Intelligence During the Cold War and Beyond (2001).
Photos by Duane Perry